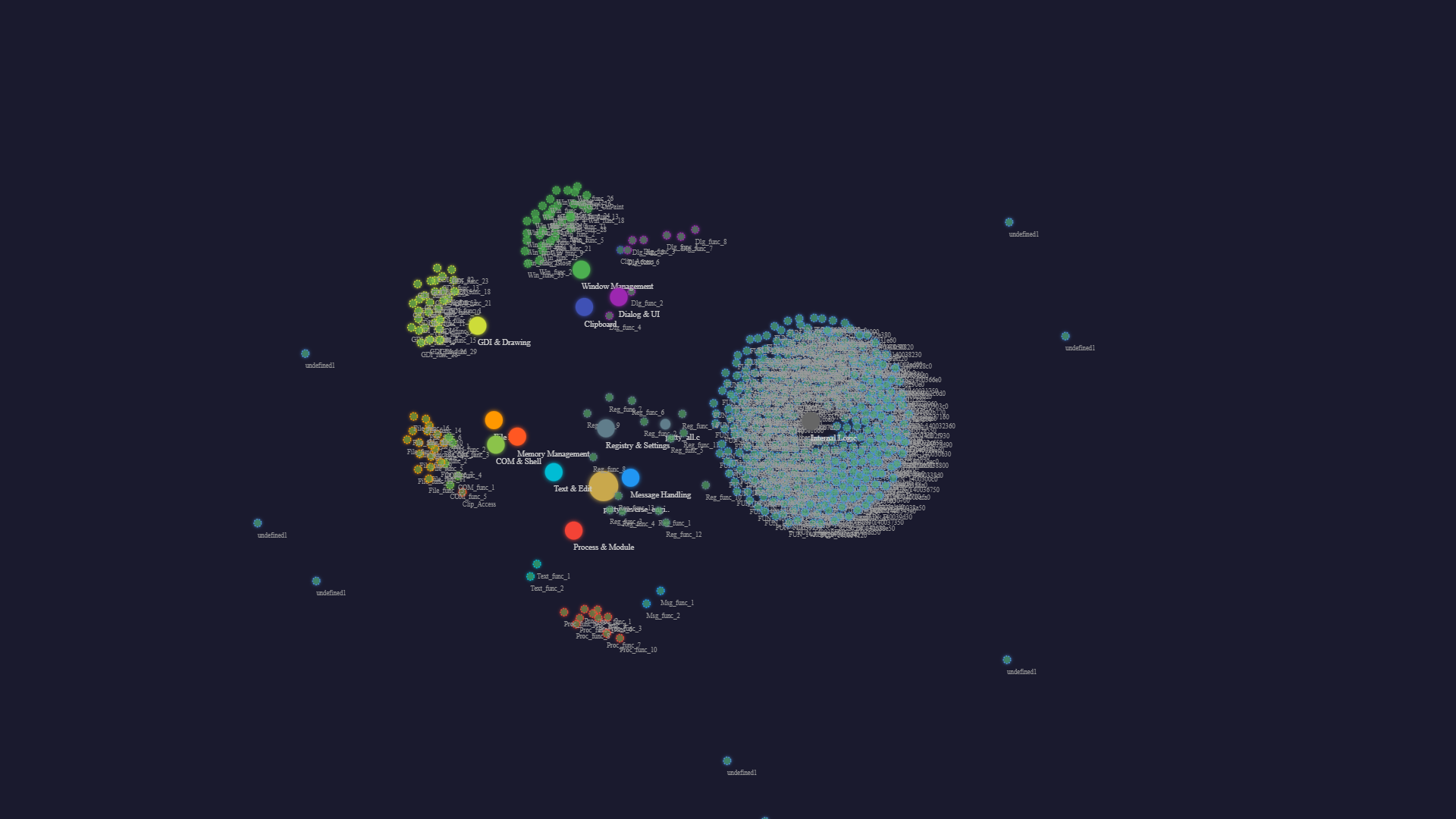
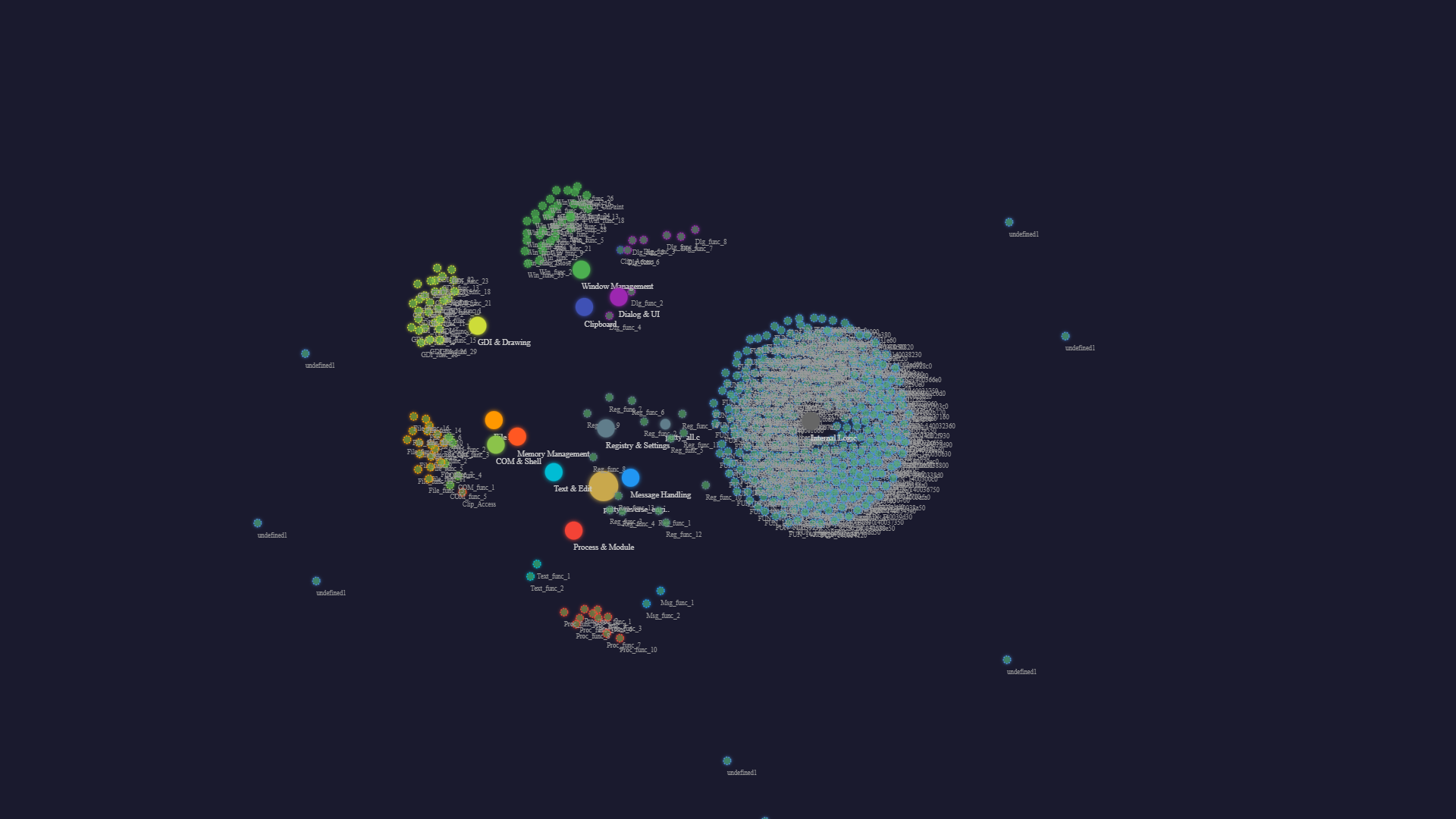
Architecture Map
The full call graph of PuTTY, extracted from a compiled binary. Every function, every dependency, every call chain. At this scale, manual analysis would take weeks. The pipeline finished in under an hour.
Enterprise Scale
One of the most widely-deployed SSH clients in the world. We decompiled the binary, extracted 2,645 functions, mapped 1,921 dependency edges, and produced a complete architecture—navigable, searchable, ready for security review.
The full call graph of PuTTY, extracted from a compiled binary. Every function, every dependency, every call chain. At this scale, manual analysis would take weeks. The pipeline finished in under an hour.
Most reverse engineering tools work on small examples. Real systems are not small.
This is not a prototype. This is the same pipeline, the same tools, applied to a codebase 27x larger than the COBOL banking demo.
Millions of lines. Decades of accumulated changes. No one who remembers how it works. That is exactly what we do.
Talk to an Engineer